Operators in the Middle East and North Africa should grow their security portfolios to boost cross-selling
01 September 2021 | Research
Article | PDF (3 pages) | Middle East and Africa Metrics and Forecasts| Cyber Security
Many operators in the Middle East and North Africa (MENA) cross-sell basic security solutions to their existing business connectivity customers.1 This approach provides a small amount of incremental revenue and helps to defend the core business, but is not sufficient to materially boost operators’ security market shares.
Challenger operators with strong ambitions to increase their share of the security market should do more to publicise their capabilities and incrementally expand their security portfolios. This article is based on Analysys Mason’s report, Approaches to providing security services to the mid-market: operator case studies in the Middle East.
The mid-market represents an opportunity for operators to expand their addressable market for security services
Security is a key driver of revenue growth for the business divisions of many operators in MENA. The mid-market2 segment provides better growth prospects than the large enterprise sector because:
- the COVID-19 pandemic has resulted in an increase in the number of cyber attacks to medium-sized enterprises because they are considered to be more vulnerable than large enterprises
- medium-sized businesses require solutions that are less-tailored and simpler than those needed by large enterprises, so less expertise is required to provide them.
Analysys Mason’s forecasts show that spending on cyber-security solutions by medium-sized businesses in MENA will grow strongly. For example, spending will grow by 7–10% in Egypt, Saudi Arabia and the UAE between 2020 and 2025 (Figure 1).
Figure 1: Security spending by medium-sized businesses, Egypt, Saudi Arabia and the UAE, 2020 and 2025
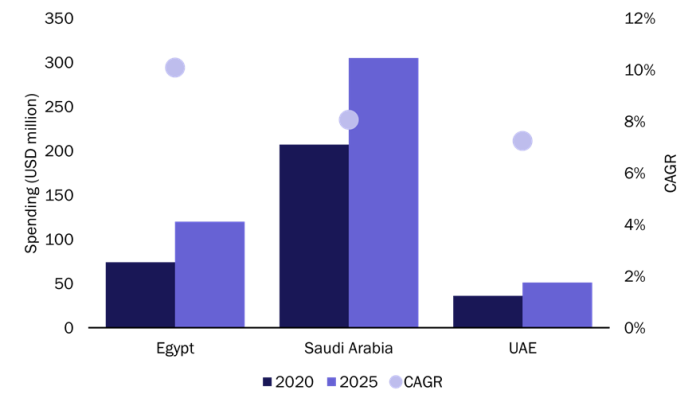
Source: Analysys Mason, 2021
Many challenger operators in MENA already offer network and endpoint security solutions as add-ons to their connectivity offerings. This will help them to protect their core connectivity business and generate incremental revenue. However, those that aim to capture a greater share of the security market and attract new customers will have to expand their security portfolios and establish new partnerships.
Operators in MENA can choose from two approaches to sell security solutions to the mid-market
Operators in the region have adopted one of two distinct strategies to sell security services to medium-sized businesses, each with advantages and disadvantages (Figure 2).
- Connectivity combined with security. Operators taking this approach primarily sell security products to their current customers, but also aim to increase their security sales to non-connectivity customers.
- Security-first. Operators implementing this strategy promote their security services independently of their connectivity business.
Figure 2: Operators’ approaches to selling security solutions to mid-market companies in the Middle East and North Africa
| Connectivity combined with security | Security-first | |
|---|---|---|
| Description | Operators build out a broad set of security products. They sell these products primarily to existing connectivity customers, but have a growing focus on selling products independently from connectivity. | Operators are focused on their sophisticated security offering instead of connectivity. |
| Examples | Omantel and stc | Etisalat and Zain |
| Advantages |
|
|
| Disadvantages |
|
|
Source: Analysys Mason, 2021
Operators have also taken different approaches to developing their security propositions and teams (including sales, support and engineering). For example, Zain developed its security capabilities organically within its B2B division. Other operators have taken a more proactive approach by acquiring or taking a large stake in specialist ICT providers. For example, Etisalat acquired Help AG, a cyber-security specialist, and Omantel established a managed cloud and security service provider, Oman Data Park, as a joint venture with a local data centre company.
Operators should publicise their capabilities and incrementally grow their security portfolios to increase their share of the market
Challenger operators that aspire to cater to the needs of medium-sized businesses in MENA can take the following actions to grow their security revenue and compete more effectively against security service providers and managed service providers (MSPs).
- Increase cyber-security awareness. Operators need to dedicate more resources to improving security education and publicising their security portfolios in order to attract new customers. For example, Help AG regularly organises webinars and publishes whitepapers to educate companies about cyber threats and explains how it can help businesses to assess, protect and respond to security attacks.
- Capitalise on the growing demand for cloud services to cross-sell managed security services. For example, Zain has invested in its security infrastructure with in-country SOCs and a local engineering and support workforce to complement its data centre capabilities. This has enabled it to cross-sell security solutions to existing cloud customers in the government and private sectors.
- Improve the sales process. Operators should have transparent pricing for their security products and should allow customers to purchase them online rather than having to visit a branch or contact a call centre. For example, Omantel publishes the prices of its ICT and security services that can be bundled with a business connectivity package on its website, and these services can be purchased online.
- Work with local partners. Operators can use their brands to build strong ties with local ICT partners, which gives them an advantage over global security players. For example, they can work with local systems integrators (SIs) and independent software vendors (ISVs) to offer consulting, customisation and integration services.
- Maintain strong links with the core business. Operators that are considering creating a separate cyber-security division (either through an acquisition or a spin-off) should ensure close collaboration between their connectivity and security divisions in order to exploit their existing sales channels and build on the trust and reputation of the parent company.
1 By “basic security solutions”, we mean endpoint, network and cloud security, consulting services and security information and event management (SIEM).
2 We define the mid-market as the market formed of companies with 100–1000 employees.
Article (PDF)
Download
